By Bharat Kapoor, Vice President, Authentix Online Brand Protection
Partnerships between major brands and social media influencers are today de rigueur. Worryingly, however, the rise of influencer marketing has been accompanied by an unseemly trend of “influencer counterfeiting”, where a minority of unscrupulous influencers blatantly hawk fake goods on the internet. A recent survey, commissioned by the UK Intellectual Property Office and conducted by the University of Portsmouth, found that “deviant” social media influencers exert a significant influence on young followers, stating a host of alarming statistics.
How Platforms Differ in Their IP Enforcement
Meta’s Current Anti-Counterfeiting Framework
While a reasonable amount of media coverage has been devoted to the trend of influencer counterfeiting, what is sometimes missed is that levels of respect for intellectual property can vary across social media platforms. For example, Meta appears to have a fairly robust complaints mechanism, with approximately 80 percent of counterfeit-related complaint resulting in takedowns (per its transparency reports). Meta has also partnered with well-known brands and initiated legal action against counterfeiters (including, in one instance, a lawsuit jointly filed with Gucci in a US court).
Why TikTok and Douyin Lag Behind
The same, however, is arguably less true for TikTok and its Chinese equivalent Douyin. Media reports, and our own enforcement experience, suggests that the extent of influencer counterfeiting on the platform is widespread and responses to takedown requests need to be improved. This also holds true for Telegram. Compounding the problem, Telegram offers users significant anonymity, thus potentially allowing rogue influencers to hide behind false identities and also evade offline enforcement actions.

Legal Action and Emerging Judicial Precedents
Amazon’s Litigation Against Influencers
Judicial precedents concerning influencer counterfeiting, and the obligations of social media platforms, remain few and far between. Late 2020, Amazon sued two influencers active on TikTok, Facebook and Instagram in the US, for allegedly working with a large network of counterfeiters to advertise and facilitate the sale of fake luxury products. The case, however, was ultimately settled on confidential terms.
The Amazon–Cartier Action Against Fake Jewelry Sellers
In June 2022, Amazon and Cartier partnered to sue an influencer selling fake jewelery on Instagram. In contrast with the earlier case, the identity of the influencer was unknown and identified in court filings only by the handle “Phym9y3v”. While the outcome of the case is eagerly awaited, a recent precedent from the Delhi High Court in India is instructive.
A Landmark Case on Platform Liability
An English-language tutor, whose lectures and course materials were being uploaded and sold on Telegram without her permission, sued Telegram for copyright infringement. The plaintiff observed that she had sent takedown requests to Telegram, but new channels with the infringing content were popping up as soon as one was disabled. Telegram contested the application on the ground that it was an intermediary and that its servers were located overseas, beyond the jurisdiction of Indian courts. The court rejected Telegram’s arguments, observing that “conventional concepts of territoriality no longer exist” and that copyright enforcement “cannot be diminished merely due to the growth of technology, which has made it easier to hide and conceal illegal activities.” The court thus directed Telegram to disclose the mobile numbers, IP addresses and email addresses used to upload and disseminate the content, along with details of the servers and networks used.
The increase in influencer counterfeiting requires brand owners to pursue rogue influencers (both online and offline) and press for myriad forms of legislative intervention and diplomatic pressure, to truly reign in influencer counterfeiting and the platforms that facilitate it.
How Brands Can Strengthen Their Online Protection Strategy
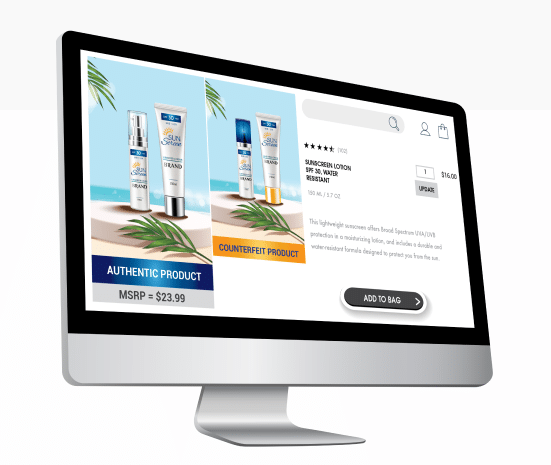
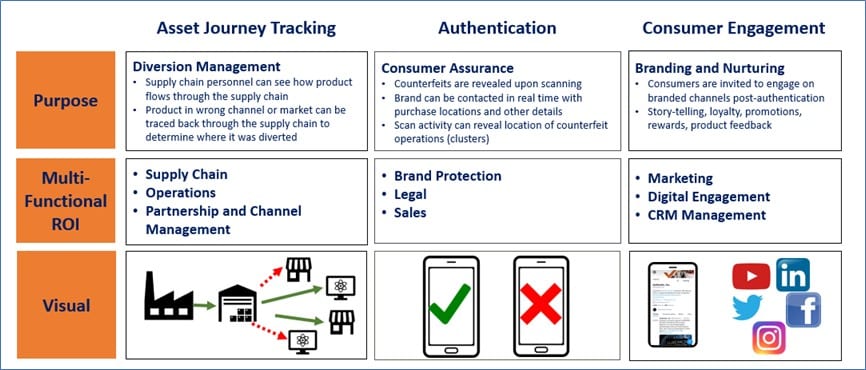
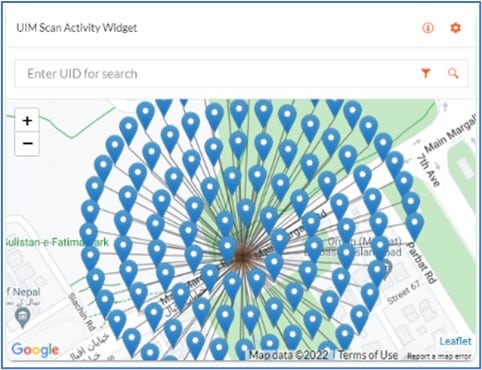
Platforms differ vastly in their responsiveness, but proactive monitoring — especially on high-risk platforms — is crucial. Technology‑driven detection, automated scanning, and AI‑powered identification help brands spot illicit listings and influencer promotions faster.
To learn more about Authentix online brand protection solutions, visit www.authentix.com/online-brand-protection.

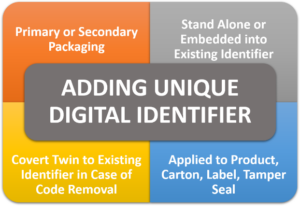

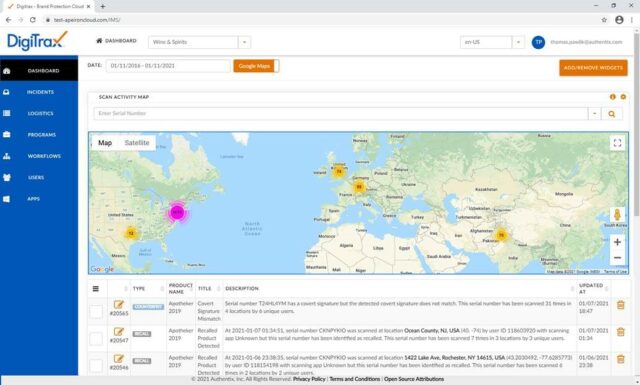

 To expand its capabilities in digital brand protection for brand owners, Authentix has recently acquired Strategic IP Information Pte Ltd (SIPI), a leading online brand and content rights protection service.
To expand its capabilities in digital brand protection for brand owners, Authentix has recently acquired Strategic IP Information Pte Ltd (SIPI), a leading online brand and content rights protection service.
 Authentix is pleased to be included in the June/July edition of
Authentix is pleased to be included in the June/July edition of  In articles
In articles